What Is Phishing in Crypto and How to Protect Yourself

Phishing attacks are a growing concern in the cryptocurrency space, as hackers target users with sophisticated methods to steal valuable assets. With the rise of digital currencies, understanding how phishing works and taking proactive steps to protect yourself is more critical than ever. In this article, we’ll explore the following: what does phishing mean, common phishing techniques and practical advice on how to stay secure.
Trade crypto on WhiteBIT Australia
What Is a Phishing Attack?
A phishing attack is a type of cybercrime where attackers attempt to trick individuals into revealing sensitive information, such as usernames, passwords, credit card details, or private keys. These attacks are typically carried out via deceptive emails, messages, or websites that appear to be from legitimate sources, like banks, online services, or even cryptocurrency platforms. The goal is to deceive the victim into clicking on malicious links or downloading infected files, which can lead to data theft, financial loss, or unauthorized access to accounts.
Phishing attacks exploit human trust, often using tactics that make the fake communication appear genuine, such as mimicking official logos, email addresses, and language patterns. In the cryptocurrency space, phishing is particularly dangerous because it can result in the theft of digital assets, which are often irreversible once transferred.
Key Differences Between Traditional Phishing and Crypto Phishing
Traditional phishing attacks typically target personal information, such as login credentials, credit card details, or social security numbers, using methods like deceptive emails, fake websites, or phone calls (vishing). The goal is to trick the victim into revealing sensitive information that can be used for identity theft or unauthorized financial transactions. These attacks are generally widespread, targeting a broad audience, and once successful, they can result in financial loss or data breaches.
Crypto phishing, on the other hand, focuses on stealing digital assets by targeting cryptocurrency users. It often involves sophisticated attacks that impersonate cryptocurrency exchanges, crypto wallet services, or popular crypto projects to steal private keys, wallet access, or login credentials. Unlike traditional phishing, crypto phishing is more specialized and can result in the irreversible loss of digital assets, as transactions made on the blockchain are difficult or impossible to reverse. These attacks exploit the growing complexity of crypto security, making them particularly dangerous for users unfamiliar with the nuances of digital asset protection.
How Does Phishing Work?
Phishing works by exploiting human trust to trick individuals into revealing sensitive information or performing actions that benefit the attacker. Here’s how it typically unfolds:
- The Initial Contact: The attacker impersonates a trusted entity, such as a bank, online service, or cryptocurrency platform. This contact often comes in the form of an email, text message, phone call, or even a pop-up on a website. The communication is designed to look legitimate, with familiar branding, logos, and sometimes even the same language patterns used by the targeted institution.
- The Deceptive Message: The phishing message usually creates a sense of urgency, fear, or excitement. For example, it might claim that your account has been compromised, that you need to verify information immediately to avoid losing access, or that you’ve won a reward and need to claim it right away. The goal is to prompt the victim to act quickly without thinking critically about the legitimacy of the message.
- Malicious Link or Attachment: The message contains a link or attachment that directs the victim to a fraudulent website or prompts them to download a malicious file. The fake website may look nearly identical to the real one, making it difficult for the victim to spot the difference. These fake sites often ask for login credentials, private keys, or other sensitive information.
- Data Harvesting: If the victim falls for the trick and enters their information (such as passwords, credit card details, or cryptocurrency wallet keys), the attacker collects this data and uses it for malicious purposes, such as stealing funds or committing fraud. In the case of crypto phishing, attackers may also gain control over a wallet or exchange account, allowing them to transfer digital assets.
- Exploitation: Once the attacker has gathered the necessary information, they can access accounts, steal funds, or engage in identity theft. In the case of cryptocurrencies, the stolen funds are typically irreversible, making the loss even more devastating.
Main Types of Phishing Attacks in Crypto
Phishing attacks in crypto take many forms, each aimed at stealing sensitive information or assets. Here are the most common types of phishing attacks:
Email Phishing
What is a phishing email?Email phishing is one of the most common methods used by cybercriminals to target crypto users. Attackers send deceptive emails that appear to come from legitimate sources, such as cryptocurrency exchanges or wallet services. These emails often contain malicious links leading to fake websites designed to steal login credentials, private keys, or other sensitive information once entered. If you receive a suspicious email, it’s crucial to know how to report a phishing email to the relevant authorities or your email provider to help prevent further attacks and protect others in the crypto community.
Examples of phishing emails:
Source: https://www.hooksecurity.co/
Scam Websites and Fake Exchanges
Scammers often create fake cryptocurrency platforms that look identical to well-known exchanges or wallet services. These fraudulent websites are designed to trick users into entering their login credentials or private keys, giving attackers access to their accounts and digital assets. Victims are typically lured to these sites through email links, social media ads, or search engine results.
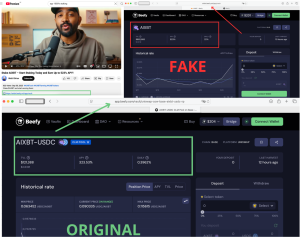
Example of a typical fake staking site. Attackers post an AI‑generated YouTube video featuring a “crypto guru” who explains in detail how to stake a memcoin for a promised 523% APY. The video description contains a link to a fake site — a slick copy of a real service but with fabricated yields, falsified contact details, and hidden scripts that request wallet permissions.
You can see the attackers copied the original site of a popular yield‑aggregator. The screenshot shows not only altered links but also inflated interest rates (fake sites usually overstate APY), and differences in UI elements and layout. Another giveaway: the social links at the bottom don’t lead to real accounts but instead prompt you to connect your wallet. The outcome is simple — once you connect, the site executes a drain: it asks you to sign a transaction or grant excessive permissions (for example, approve asset management), and after you confirm, funds are immediately transferred to addresses controlled by the scammers.
Social Media & Messaging Apps
Phishing attacks on social media and messaging platforms like Telegram or Discord are increasingly common in the crypto space. Attackers often impersonate reputable crypto influencers, exchanges, or community members to promote fake investment opportunities, airdrops, or customer support services. These phishing and scams encourage users to provide sensitive information or send funds to fake addresses.
Malicious Smart Contracts & Token Traps
In the world of decentralized finance (DeFi), attackers may trick users into interacting with malicious smart contracts or fake tokens. These contracts may execute unwanted transactions, steal funds, or lock users’ assets. Often, scammers entice victims through social media, messaging apps, or fake investment opportunities involving newly launched tokens, leading them to unknowingly approve malicious transactions.
Airdrop & Giveaway Scams
Airdrop and giveaway scams are particularly common in the cryptocurrency community. Attackers promote fake airdrops or giveaways, claiming that users need to provide their wallet address or private keys to claim the rewards. These scams prey on users’ desire for free tokens, and once victims share their information, attackers can steal their funds or compromise their wallets.
Vishing & Smishing in Crypto
Vishing (voice phishing) and smishing (SMS phishing) are tactics used to target crypto users via phone calls or text messages. In vishing, attackers impersonate customer support representatives from exchanges, urging victims to reveal sensitive information or approve fraudulent transactions. Smishing attacks often involve text messages that lead victims to malicious links or fake websites, where they are tricked into entering their personal details or wallet credentials.
The Evolution of Phishing: From Spam to AI
The evolution of phishing has seen a significant shift from simple spam emails to highly sophisticated attacks powered by artificial intelligence (AI). Initially, phishing involved mass emails that were often generic, poorly crafted, and sent to thousands of random recipients. These early attempts were easy to spot due to their obvious signs of fraud, such as misspellings, strange URLs, and unprofessional formatting. However, over time, phishing tactics became more refined as cybercriminals learned to craft convincing messages and mimic trusted entities, such as banks and online retailers.
In recent years, the rise of AI and machine learning has taken phishing to a new level of sophistication. AI tools can now generate highly personalized and convincing phishing messages based on detailed data about individuals, often gathered from social media or previous interactions. These advanced attacks are harder to detect and can be tailored to each victim, making them more effective at tricking users. AI-powered phishing can also be used to create deepfake voice calls or videos, further enhancing the believability of the scam. As technology continues to evolve, the line between legitimate communication and phishing becomes increasingly blurred, requiring users to be more vigilant than ever in identifying threats.
Real-World Cases from the Crypto Market
Here are several real-world cases highlighting the prevalence and sophistication of phishing and crypto-related scams:
- $3 Million Phishing Loss from a Single Click. An investor lost $3 million in USDT after unknowingly signing a malicious blockchain transaction. The attacker had disguised the contract address, making it appear legitimate. This incident underscores the risks of not thoroughly verifying transaction details before approval.
- $91 Million Phishing Scam. In August 2025, a significant phishing attack resulted in a loss of $91 million. This was part of a broader surge in crypto hacks, with a total of $173 million lost due to exploits that month.
- $48 Million in Stolen Tokens to Phishing. A hacker who had previously exploited the UXLINK blockchain and minted $48 million worth of tokens fell victim to a phishing attack. The stolen funds were lost to another scammer using common phishing tactics, highlighting that even cybercriminals are not immune to fraud.
- $341 Million Lost to Fake Social Media Accounts. Scammers created fake accounts on social media platforms, leading to record-setting crypto phishing attacks that resulted in $341 million in losses. The top 20 victims lost over $58 million, with many incidents caused by phishing attacks involving offline authorization signatures.
- $5 Billion Bitcoin Scam in the UK. Zhimin Qian, a Chinese national, orchestrated a scam that defrauded 128,000 people between 2014 and 2017. She converted the stolen funds into Bitcoin, which were later seized in the UK, marking one of the largest cryptocurrency seizures in history.
How to Prevent Phishing Attacks?
Here are the 5 key points of how to avoid phishing attacks:
- Verify URLs and Email Addresses: Always double-check website URLs and email addresses to ensure they are legitimate. Phishing sites often use URLs that closely resemble trusted platforms but contain subtle errors.
- Enable Two-Factor Authentication (2FA): Protect your crypto accounts with 2FA. This adds an extra layer of security, making it harder for attackers to access your accounts even if your password is compromised.
- Use Cold Storage for Large Amounts: For significant cryptocurrency holdings, use cold storage solutions like hardware wallets. These offline wallets provide superior protection from phishing attacks and online threats.
- Be Wary of Unsolicited Offers: Avoid sharing personal information or private keys in response to unsolicited offers, such as investment opportunities, giveaways, or airdrops. These are common phishing tactics.
- Educate Yourself and Stay Updated: Phishing techniques evolve rapidly. Stay informed about the latest scams and trends in the crypto space. Follow official project channels and cybersecurity experts to stay ahead of emerging threats.
What to Do If You’ve Fallen Victim?
If you’ve fallen victim to a phishing attack, act quickly to minimize the damage. Immediately change your passwords on any affected accounts, and if possible, revoke access to any unauthorized transactions or services. If you have shared private keys or seed phrases, move your funds to a secure wallet without delay. Contact the customer support teams of any affected platforms to report the incident and ask for assistance in securing your account. Additionally, notify your bank or financial institution if your financial details were compromised. Lastly, consider filing a report with relevant authorities, such as local law enforcement or a cybercrime unit, to help track and prevent future attacks.
Report the scam to ScamWatch.
See the price of cryptocurrency on the market
Conclusion
Phishing attacks in the crypto space are becoming increasingly sophisticated. By staying informed, using security measures like 2FA, and keeping your private keys safe, you can reduce the risk of falling victim to scams. Always verify the authenticity of communications and stay cautious when interacting online.